C Generate An Api Key
Note: If you generate API keys for a user that already has API keys, the old keys will be replaced. If you delete existing keys or generate new API keys for a user, Tenable.sc deauthorizes API requests attempted with the old keys. Before you begin: Enable API keys to allow users to perform API key authentication, as described in Enable API Key. Full API reference for the API Key resource in the Twilio API. Learn how to create, fetch (get), read (list), and update API Keys to authenticate to the REST API and create and revoke access tokens.
by Ramesh Lingappa
We all know how valuable APIs are. They’re the gateway to exploring other services, integrating with them, and building great solutions faster.
You might have built or are thinking of building APIs for other developers to use. An API needs some form of authentication to provide authorised access to the data it returns.
There are several authentication standards available today such as API Keys, OAuth, JWT, etc.
In this article, we’ll look at how to correctly manage API Keys to access APIs.
So Why API Keys?
API Keys are simple to use, they’re short, static, and don’t expire unless revoked. They provide an easy way for multiple services to communicate.
If you provide an API for your clients to consume, it’s essential for you to build it in the right way.
Let’s get started, and I’ll show you how to build API Keys the right way.
API Key Generation
Since the API key itself is an identity by which to identify the application or the user, it needs to be unique, random and non-guessable. API keys that are generated must also use Alphanumeric and special characters. An example of such an API key is zaCELgL.0imfnc8mVLWwsAawjYr4Rx-Af50DDqtlx.
Secure API Key Storage
Since the API key provides direct access to data, it’s pretty much like a password that a user of a web or mobile app provides to gain access to the same data.
Think about it. The reason we need to store API keys is to make sure that the API key in the request is valid and issued by us (just like a password).
We don’t need to know the raw API key, but just need to validate that the key is correct. So instead of storing the key in plain text (bad) or encrypting it, we should store it as a hashed value within our database.
A hashed value means that even if someone gains unauthorised access to our database, no API keys are leaked and it’s all safe. The end user would send the raw API key in each API request, and we can validate it by hashing the API key in the request and compare the hashed key with the hash stored within our database. Here is a rough implementation of it in Java:
In the code above, the primary key will be a combination of the prefix and the hash of the API key {prefix}.{hash_of_whole_api_key}.
But hold on, there is more. Storing a hashed value brings specific usability problems. Let’s address those now.
Presenting the API Key to users
Since we don’t store the original API key, we can show it only once to the user, at the time of creation. So be sure to alert users that it cannot be retrieved again, and they need to generate a new token if they forget to copy the API key and store it safely. You can do something like this:
How users can identify a generated API Key later
Another problem is how users identify the right API key in your console if they need to edit or revoke it. This can be solved by adding a prefix to the API key. Notice in the picture above the first 7 characters (that’s our prefix), separated by the dot.
Now you can store this prefix in the database and display it in the console so users are able to quickly identify the right API key entry, like this:
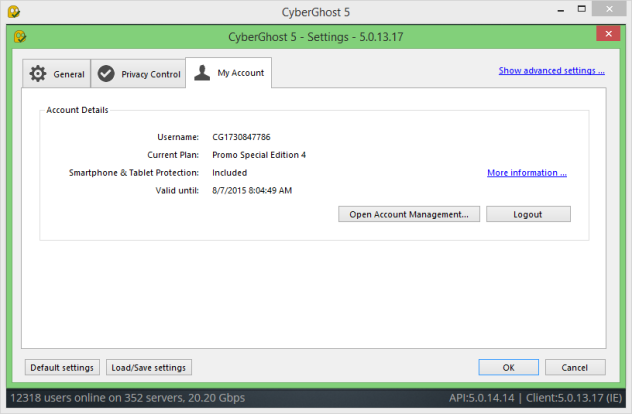 Jan 26, 2020 CyberGhost VPN 7.2.4294 Crack Torrent 2019. Cyberghost crack is a software that has been developed to try and provide solutions to online security challenge among many other functions. It provides a number of solutions such as for torrenting or browsing privately/anonymously. Using this software your content as well as identity is protected. CyberGhost VPN Keygen works across multiple devices, with apps for Windows, Mac, iOS, Android, Linux and Routers, and even supports simultaneous connections on up to 7 devices so you’ll always be protected. With the highest possible speed and unlimited bandwidth and traffic, you can browse freely using CyberGhost VPN License Key. Nov 23, 2015 The security providing network is CyberGhost VPN 5 Premium Key 2015 included. When clients want to gain something provided by key supplier they can dial up another Cyber Ghost VPN IP address on their interface. Nov 20, 2015 The security providing network is CyberGhost VPN 5 Premium Crack 2015 included. When clients want to gain something provided by crack supplier they can dial up another Cyber Ghost VPN IP address on their interface. CYBERGHOST VPN 5 CRACK PREMIUM, SERIAL KEY FULL DOWNLOAD gives you security from thefts, internet hijackers, and hackers. CyberGhost 5 is very useful. Mar 07, 2020 CyberGhost VPN Premium Crack 2020 Cyberghost Premium VPN Crack is the latest program that offers privacy in various sites and online assets. Besides, This program allows you to visit any site, therefore, change the customer’s original IP address.
Jan 26, 2020 CyberGhost VPN 7.2.4294 Crack Torrent 2019. Cyberghost crack is a software that has been developed to try and provide solutions to online security challenge among many other functions. It provides a number of solutions such as for torrenting or browsing privately/anonymously. Using this software your content as well as identity is protected. CyberGhost VPN Keygen works across multiple devices, with apps for Windows, Mac, iOS, Android, Linux and Routers, and even supports simultaneous connections on up to 7 devices so you’ll always be protected. With the highest possible speed and unlimited bandwidth and traffic, you can browse freely using CyberGhost VPN License Key. Nov 23, 2015 The security providing network is CyberGhost VPN 5 Premium Key 2015 included. When clients want to gain something provided by key supplier they can dial up another Cyber Ghost VPN IP address on their interface. Nov 20, 2015 The security providing network is CyberGhost VPN 5 Premium Crack 2015 included. When clients want to gain something provided by crack supplier they can dial up another Cyber Ghost VPN IP address on their interface. CYBERGHOST VPN 5 CRACK PREMIUM, SERIAL KEY FULL DOWNLOAD gives you security from thefts, internet hijackers, and hackers. CyberGhost 5 is very useful. Mar 07, 2020 CyberGhost VPN Premium Crack 2020 Cyberghost Premium VPN Crack is the latest program that offers privacy in various sites and online assets. Besides, This program allows you to visit any site, therefore, change the customer’s original IP address.
Don’t give the API Key all the power
One common mistake that API key providers make is providing one key to access everything, since it’s easy to manage. Don’t do that. Assume that a user just needs to read an email, and generates an API key. But that key now has full access to other services, including deleting records in the database.
The right approach is to allow the end users to properly restrict API Key access and choose specific actions that an API key can carry out. This can be done by providing scopes, where each scope represents a specific permission.
For example,
- if you need an API key to just send emails, you can generate an API key with the scope as “email.send”
- if the end user has multiple servers and each carries out a specific action, then a separate API key can be generated with a specific scope.
So while creating the API key, allow users to select what access that API key should have, as in the image below. Putty windows generate ssh key.
This way users can generate multiple API keys, each with specific rules of access for better security. And when an API request is received, you can check if the API Key has the right scope to access that API. Now the database looks something like this:
Rate limiting API keys
Yes, you might already know it, but it is important to rate limit requests made with specific API Keys to ensure no bad actor can take down your API servers or cause performance issues that affect your other customers. Having a proper rate limiting and monitoring solution keeps the API service healthy.
Conclusion
API keys, when built right, are still a great way to communicate with another server. As we reviewed in this article, following certain practices offers benefits to both API consumers and API providers. Hope this helps you.
Happy Securing your APIs!
New Users: Before you can start using the Google Maps Platform APIs and SDKs, you must sign up and create a billing account.To learn more, see Get Started with Google Maps Platform.To use the Maps Embed API you must have an API key. The API key is a unique identifier that isused to authenticate requests associated with your project for usage and billing purposes.
Get the API key
You must have at least one API key associated with your project.
To get an API key:
- Visit the Google Cloud Platform Console.
- Click the project drop-down and select or create the project for which you want to add an API key.
- Click the menu button and select APIs & Services > Credentials.
- On the Credentials page, click Create credentials > API key.
The API key created dialog displays your newly created API key. - Click Close.
The new API key is listed on the Credentials page under API keys.
(Remember to restrict the API key before using it in production.)
Add the API key to your request
You must include an API key with every Maps Embed API request.In the following example, replace YOUR_API_KEY withyour API key.
For more information about MODE and parameters options in the code above, see Forming the URL for the Maps Embed API.
Restrict the API key
We strongly recommend that you restrict your API key. Restrictions provide added security and helpensure only authorized requests are made with your API key. There are two restrictions. You shouldset both:
C Generate An Api Key Login
- Application restriction: Limits usage of the API key to either websites (HTTP referrers), web servers (IP addresses), or mobile apps (Android apps or iOS apps). You can select only one restriction from this category, based on the platform of the API or SDK (see GMP APIs by Platform).
Note: If you need to call web, web service, and/or mobile APIs from the same (client-side) app, create and restrict multiple keys.
- API restriction: Limits usage of the API key to one or more APIs or SDKs. Requests to an API or SDK associated with the API key will be processed. Requests to an API or SDK not associated with the API key will fail. (The API or SDK must be enabled and must support the application restriction.)
To restrict an API key:
What Is An Api Key
- Go to the Google Cloud Platform Console.
- Click the project drop-down select the project that contains the API key you want to secure.
- Click the menu button and select APIs & Services > Credentials.
- On the Credentials page, click the name of the API key that you want to secure.
- On the Restrict and rename API key page, set the restrictions:
- Application restrictions
- Select HTTP referrers (web sites).
- Add the referrers.
- API restrictions
- Select Restrict key.
- Click Select APIs and select Maps Embed API.
(If the Maps Embed API is not listed, you need to enable it.) - Click SAVE.